what a proxy is (educational, non-abuse)
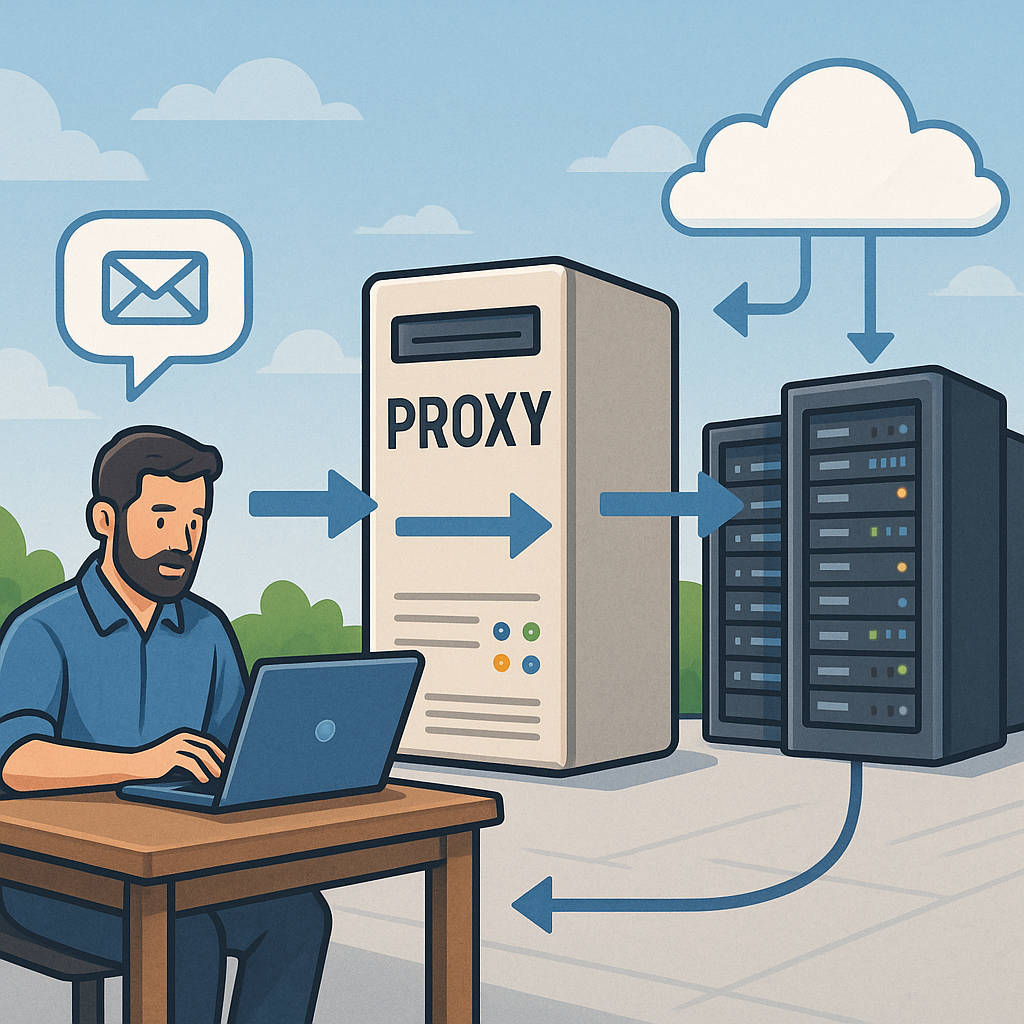
A proxy is an intermediary service that sits between a client and another server, relaying requests and responses while offering a point for control and observation. For beginners it helps to think of a proxy as a receptionist for network traffic that can accept a request, check or modify it, and then forward it on behalf of the original sender. This intermediary role is useful across many parts of infrastructure because it separates direct access to resources from the actors that request them, enabling policies and features that would be hard to implement on every client or every backend server.
There are two high-level categories of proxy to be aware of: forward proxies and reverse proxies. A forward proxy is used by clients to reach other servers and is common in corporate environments that centralise and control outbound traffic. A reverse proxy sits in front of one or more backend servers and accepts incoming client requests, often performing tasks such as load distribution, caching, or TLS termination before passing traffic to the internal service. Understanding this distinction clarifies why proxies appear in different places of a network architecture and why they offer different benefits.
Proxies come in different technical flavours that suit particular needs. HTTP proxies operate at the HTTP layer and can inspect and modify headers and bodies, while SOCKS proxies are protocol-agnostic and work at a lower level, forwarding arbitrary TCP traffic. Transparent proxies intercept traffic without requiring client configuration and are often used for caching or inspection, whereas explicit proxies require clients to be configured to use them. Reverse proxies often combine multiple features such as load balancing, health checks, caching, compression, and TLS offload. Each type has design trade-offs around visibility, control, and performance.
Common reasons organisations deploy proxies include enhancing security, improving performance, and simplifying operations. Security benefits arise because a proxy can enforce authentication, apply access controls, filter malicious content, and centralise logging for audit and incident response. Performance gains come from caching frequently requested content close to clients, reducing latency and backend load, and from compressing responses to save bandwidth. From an operational perspective, a reverse proxy decouples deployment and scaling of backend services from public endpoints, making rolling updates and blue–green deployments easier to manage.
- Load balancing to distribute requests across servers for reliability and capacity improvements.
- Caching to reduce repeated work and speed up common requests for users.
- TLS termination to centralise certificate management and reduce CPU load on application servers.
- Access control and auditing to apply consistent policies and collect logs in one place.
- Protocol translation or gateway functions for legacy systems and microservices.
When considering a proxy for infrastructure use, there are practical considerations to weigh. Proxies can introduce additional latency and become a single point of failure if not deployed in a highly available configuration. They also centralise logs and metadata, so planning for storage, retention and proper access controls is essential for privacy and compliance. Monitoring and observability of the proxy itself are vital, because problems at that layer can affect many services. Finally, think about scaling and automation: ensure your proxy layer can be configured and updated safely as traffic patterns change.
If you are new to this area, start by mapping where intermediaries already exist in your environment and what problems they are solving, then experiment with a non-production reverse proxy to see features such as caching and TLS offload in action. For further practical reading on related infrastructure topics, see this collection of posts that cover deployment patterns and operational considerations for network components like proxies at Build & Automate Infrastructure posts. Proxies are a common, useful part of modern infrastructure when used responsibly and with attention to security, performance and compliance. For more builds and experiments, visit my main RC projects page.
Comments
Post a Comment